Cyberattack
Impacting Digital's systems are locked. The attacker left no
name — only clues.
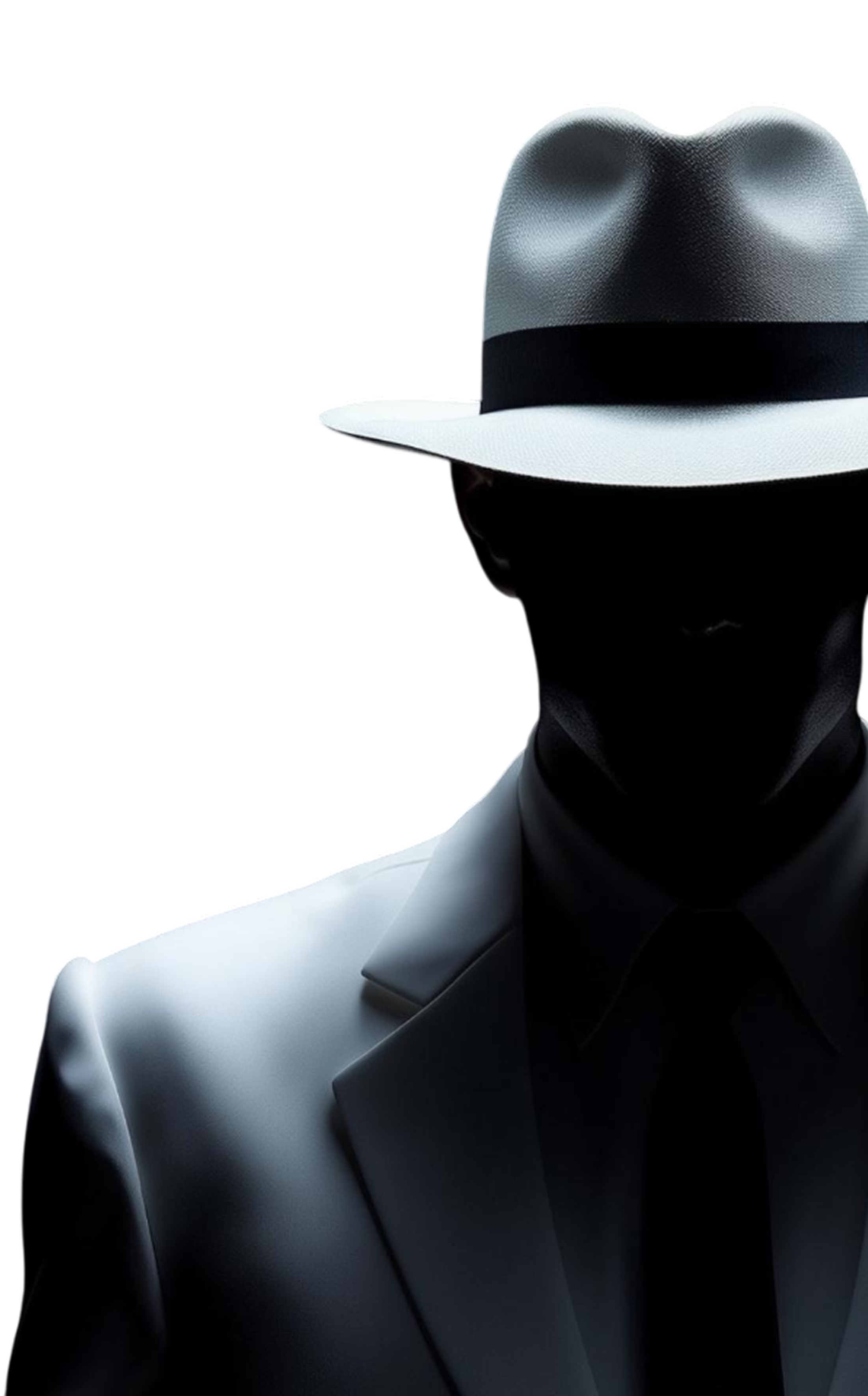
In Cyberattack, you step into the role of a digital investigator, guided by White Hat, your trusted mission assistant. Your task? Reconstruct the attack, follow the traces, and expose who hacked the system — and how.
Solve real-world-inspired cybersecurity challenges, recover lost data, and uncover the final encrypted message that reveals the truth.
8 challenges. 1 hacker. Can you stop them before it’s too late?
In Cyberattack, you step into the role of a digital investigator, guided by White Hat, your trusted mission assistant. Your task? Reconstruct the attack, follow the traces, and expose who hacked the system — and how.
Solve real-world-inspired cybersecurity challenges, recover lost data, and uncover the final encrypted message that reveals the truth.
8 challenges. 1 hacker. Can you stop them before it’s too late?

🗔
Message from White Hat
✕
Are you ready to help me?
Register now and complete the mission.
Register now and complete the mission.